LinuxU Laptop (Admin)
- SSH / config / docs
- Primary control node
- Remote management
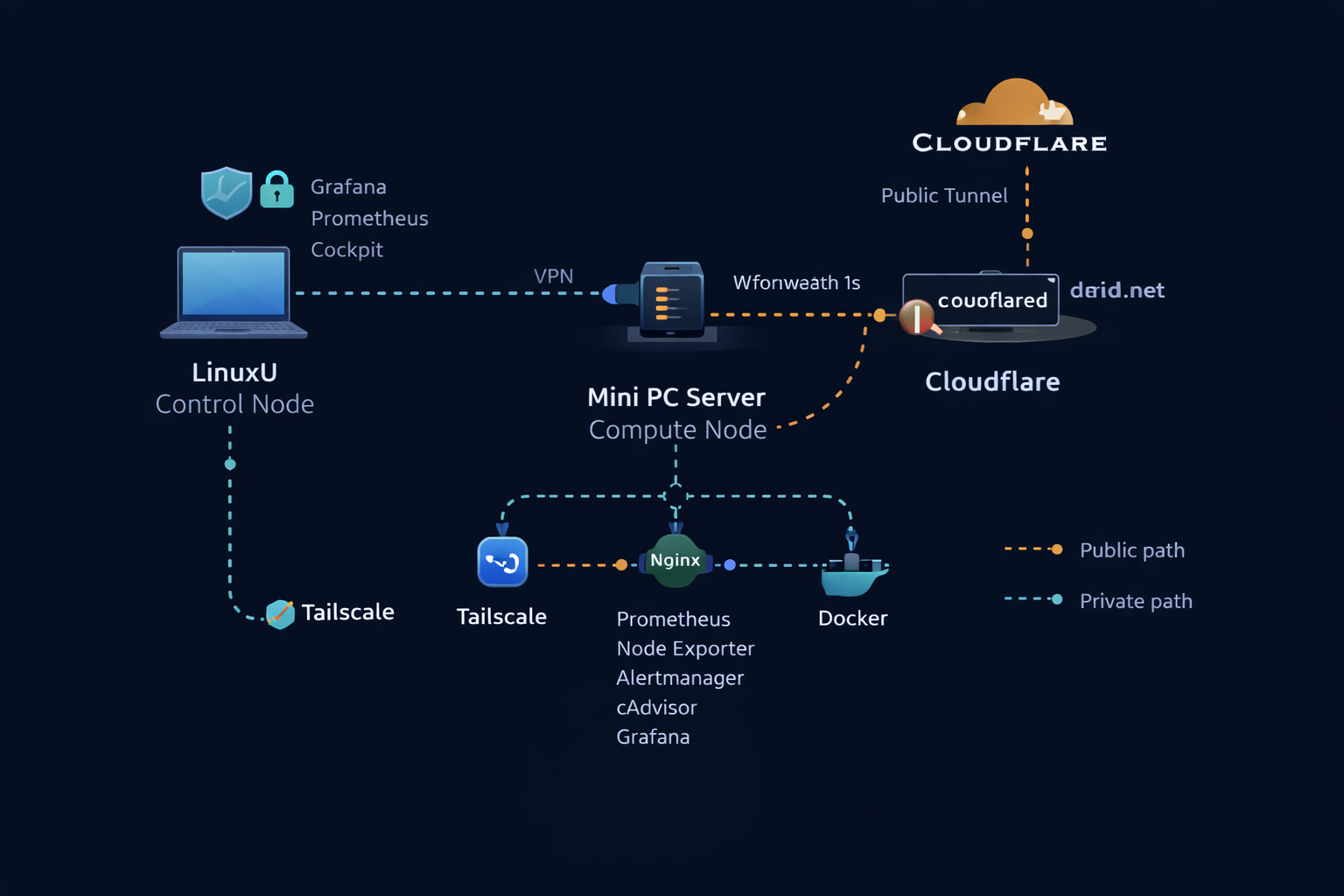
Hardware, services, and monitoring stack for dlbuild.net — designed for safe public publishing (static only) while keeping admin endpoints private.
High-level view of the lab network, secure access path, and monitoring stack layout.
Tip: open image in a new tab to zoom.
Hands-free monitoring console with alerting and kiosk automation.
Triage notes, fixes, and runbooks captured during lab operations.
During kiosk/GUI experimentation (XFCE/LightDM), the Mini drifted from a headless server posture, introducing login/keyring noise and a confusing secondary user (dashboard). We re-hardened the host by switching the default boot target back to multi-user.target and disabling LightDM, while verifying the monitoring stack remains stable and reachable via Tailscale-only bindings.
Power On
→ Ubuntu boots (multi-user.target)
→ Docker starts
→ Containers auto-recover (unless-stopped)
→ Monitoring stack available via tailscale
sudo systemctl status nginx
sudo systemctl status docker
docker compose ps
df -h
free -h
uptimeTip: keep these checks “muscle memory.” If something is off, grab logs next and write the verified fix.